Your Social Media Fingerprint
Without your consent most major web platforms leak whether you are logged in. This allows any website to detect on which platforms you're signed up. Since there are lots of platforms with specific demographics an attacker could reason about your personality, too.
Demonstration
You are logged in to:
No platform
(or maybe you've disabled third party cookies, or you are using something like Privacy Badger?)
You are not logged in to:
Explanation
For most web platforms there's a way to abuse the login mechanism to detect whether a user is logged in to that service.
Although this vulnerability is well known for several years most companies won't fix it.
The exploit is pretty simple and actually easy to fix. Let's look at facebook.com to get an idea of how it works:
How does the login redirect mechanism work?
At first we need to understand the login redirect mechanism. Say you're logged in and visit
https://www.facebook.com/bookmarks/pagesNow if you open this URL in a private tab where you are not logged in, you will get redirected to the login screen with this URL:
https://www.facebook.com/login.php?next=https%3A%2F%2Fwww.facebook.com%2Fbookmarks%2Fpagesnext parameter in the URL: https%3A%2F%2Fwww.facebook.com%2Fbookmarks%2Fpages.
That's the URL we came from and it is used to redirect us back there once we've logged in.
But if we enter the login URL in a browser tab where we are already logged in, we get redirected without getting prompted to login. Therefore this URL returns:
- If logged in: the resource at the URL in the
nextparameter - If logged out: the login screen
Bypass the Same Origin Policy
How does this URL help us? The Same Origin Policy prevents to read the results of this request from any other domain but https://facebook.com...
Well, the SOP is strict for HTML pages, but it allows to receive images from other origins! So if the resource in the next parameter would be an image we could read it from our website. It can't be any image though. Facebook checks if the URL in the next parameter starts with https://facebook.com. So we need to find an image on facebook.com. Should be easy, right? Actually it isn't, because facebook hosts almost all images on their CDN servers under the domain fbcdn.net. Though there is one image that you can find on almost every webserver: the good old favicon.ico!
This is how our login URL looks like with the favicon as next parameter:
https://www.facebook.com/login.php?next=https%3A%2F%2Fwww.facebook.com%2Ffavicon.ico- Logged in: returns the favicon image
- Logged out: returns the HTML of the login page
We can use this URL in an <img> tag in our website:
<img src="https://www.facebook.com/login.php?next=https%3A%2F%2Fwww.facebook.com%2Ffavicon.ico"><img> tag's property:
- Logged in: receives the favicon image, will load it successfully, and the
onLoadcallback will be fired. - Logged out: receives the HTML of the login screen, will fail to load it as an image, and the
onErrorcallback will be fired.
<img onload="alert('logged in to fb')" onerror="alert('not logged in to fb')" src="https://www.facebook.com/login.php?next=https%3A%2F%2Fwww.facebook.com%2Ffavicon.ico">Other Platforms
This mechanism works for almost all major web platforms, because they all have a redirect parameter in their login endpoint and they need to host their favicon on their domain (bc of browser compatibility, and of the technical debt of the former lack of standards).
Updates
- 2016/10/07: Instagram removed the favicon from their root domain and host their favicon on their CDN now.
- 2016/10/14: Stackoverflow has fixed the issue.
- 2016/10/14: It looks like Firefox has fixed the issue at least for the major networks with their default tracking protection blacklist (The blacklist comes from https://disconnect.me/).
Console screenshot of the errors when visting socialmedia-leak with current Firefox: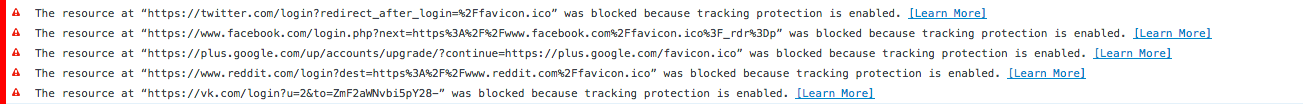 Though it probably still works for all platforms where you don't see a broken image
Though it probably still works for all platforms where you don't see a broken image instead of a logo.
- 2016/10/14: Netflix now just redirects to the main browse page regardless of the redirect in the URL.
- 2017/11/29: Flickr has fixed the issue, too.
Further Attacks
This attack could be a step of a worse attack such as deanonymization techniques, Clickjacking, Profilejacking, or Phishing where it is crucial to know if a victim is logged in to a service.
Protection
First of all: disable third party cookies.
You can also install a browser plugin like Privacy Badger, or uMatrix to protect yourself from this attack.
For further information see the discussion on Hackernews or this discussion on Reddit.
Help to solve the issue!
The companies won't fix the issue, because the risk for their own service is relatively low. Though so many platforms are vulnerable to this, it becomes a real privacy issue. Please help to raise awareness to push the companies to fix the issue.
- Share this demo on Twitter
- Share this demo on Facebook
- Share this demo on Google+
- Share this demo via Whatsapp
- Star this project on Github
If you find more web platforms that are vulnerable to this attack, please file an issue to add it. The more complete this list is, the bigger the issue and the higher the pressure for platforms to fix it.
If you like this page maybe you like my other works, too:
- Snapdrop: Instantly share files with devices nearby. No Setup, No Signup.
- Webkay: A demonstration of all the personal information your browser is leaking.
- Ubercookie: An irrevocable persistent browser cookie.
- Web Security Quiz: Test your knowledge with OWASP exam questions
- Capira: Interactive Learning Videos
- Facebook: Like my page to get updates about the stuff I create
- Twitter: Follow me on Twitter to get updates about the stuff I create